Six Common Pitfalls to Avoid When Implementing a Zero Trust Model
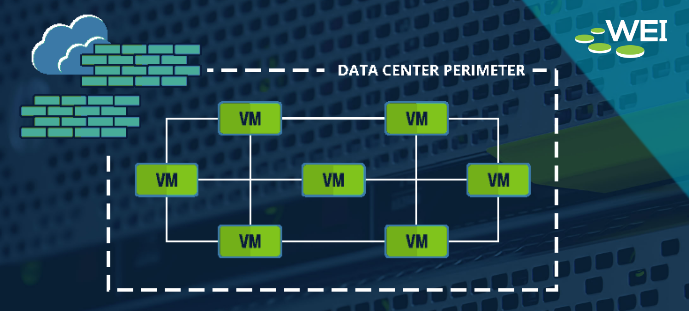
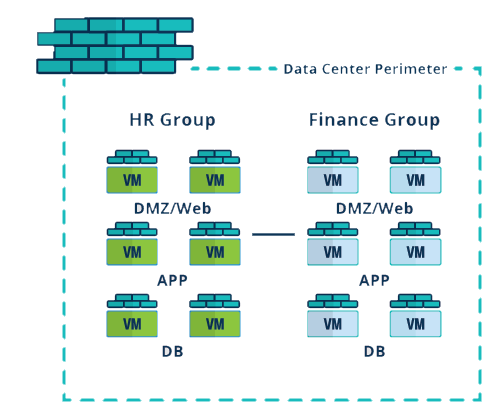
Zero Trust is more than just a cybersecurity buzzword, it is an essential security model for enterprises looking to safeguard their networks, data, and critical systems. With cyber threats becoming more persistent and sophisticated, traditional security approaches that rely on perimeter defenses are no longer sufficient. The Zero Trust model shifts the focus from implicit trust to continuous verification, ensuring that users, devices, and applications are authenticated and authorized before accessing resources.