Data center architectures have continually evolved to meet the needs of mobile, social, big data, and cloud applications--and enterprise security solutions have evolved as well to support the new security needs of these applications in distributed data centers.
Attacks on data centers are increasing, and physical security appliances aren’t sufficient to stop them. Independent research shows that successful attacks are occurring with growing regularity, and at increasing costs to enterprises. Seventy-five percent of all attacks begin stealing data in a matter of minutes, and may not be detected for quite a while. Additionally, after an attack has been discovered, full containment and repair can take weeks. There is no question that a new model for data center security is needed before these attacks become unstoppable.
Micro-Segmentation adds additional security
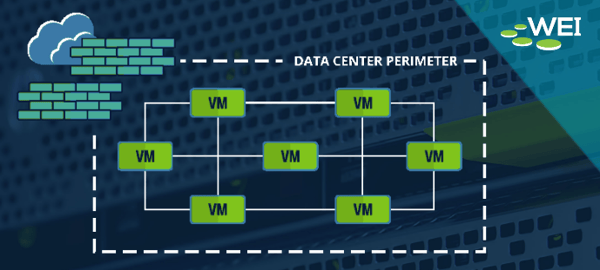
Micro-segmentation is a method of creating secure zones in data centers and cloud deployments that allows companies to isolate workloads from one another and secure them individually. It’s aimed at making network security more granular.
While traditional firewalls, intrusion prevention systems, and other security systems are designed to inspect and secure traffic coming into a data center from outside, micro-segmentation gives enterprises greater control over the growing amount of lateral communication that occurs between servers. This communication bypasses perimeter-focused security tools and has traditionally been vulnerable to attack.
Cisco lists the following goals for micro-segmentation:
- Programmatically define segments on an increasingly specific basis, achieving greater flexibility (for example, limit the lateral movement of a threat or quarantine a compromised endpoint within a broader system)
- Automatically program segments and policy management across the entire application lifecycle (from deployment to decommissioning)
- Enhance security and scalability by enabling a zero-trust approach for heterogeneous workloads.
Bonus Tech Brief: Using Network Segmentation to manage Malware and Ransomware Risks
3 Security Solutions for micro-segmentation
Here are three networking security solutions enterprises should consider.
Cisco ACI
Cisco ACI (Application Centric Infrastructure) uses a new application-aware construct called an endpoint group that allows application designers to define the endpoints that belong to the EPG regardless of their IP addresses or the subnets to which they belong. The endpoint can be a physical server, virtual machine, Linux container, or even traditional mainframe computers.
With Cisco ACI’s highly specific endpoint security enforcement, customers can dynamically enforce forwarding and security policies, quarantine compromised or rogue endpoints based on virtual machine and network attributes, and restore cleaned endpoints to the original EPG.
Additionally, while data center micro-segmentation can provide enhanced security for lateral traffic within the data center, its true value lies in its integration with application design and holistic network policy, and it must interoperate transparently with a wide variety of hypervisors, bare-metal servers, L4-L7 devices, and orchestration platforms.
VMware NSX
VMware NSX (Network virtualization and security platform) micro-segmentation meets security recommendations made by the National Institute of Standards and Technology (NIST) in providing the ability to utilize network virtualization-based overlays for isolation, and distributed kernel-based firewalling for segmentation through ubiquitous centrally managed policy control. It also uses higher-level components or abstractions in addition to the basic 5-tuple for firewalling.
As a security platform, NSX based micro-segmentation goes beyond NIST recommendations and enables the ability for fine-grained application of service insertion where they are most effective: as close to the application as possible in a distributed manner while residing in separate trust zones outside the application’s attack surface.
Free Infographic: See how micro-segmentation works
Finally, for physical to physical communication, NSX can tie automated security of physical workloads into micro-segmentation through centralized policy control of those physical workloads through the NSX Edge Service Gateway or integration with physical firewall appliances. This allows centralized policy management of your static physical environment in addition to your micro-segmented virtualized environment.
Illumio
The Illumio Adaptive Security Platform (ASP) makes the invisible visible by mapping out connections between workloads in a single application, as well as connections between the applications themselves. This may reveal connections between systems that you weren’t aware of before and helps identify risks that weren’t immediately obvious.
Illumio uses this map of network traffic to automatically generate micro-segmentation policies for every workload and application running anywhere, on any computer platform, and analyze them in seconds – saving security teams critical time, reducing the risk of human error and improving policy consistency across the network.
The Takeaway
Micro-segmentation offers significantly more visibility and policy granularity than network or application segmentation, including the ability to fully visualize the environment and define security policies with process-level precision. This added granularity is increasingly important as growing use of cloud services renders traditional network-based security boundaries ineffective and elevates the urgency of detecting and stopping lateral movement
Are you looking for additional information on how to up your security game to meet the needs of your organization? Contact the network security experts at WEI for an unbiased perspective to solving your enterprise’s security challenges.
NEXT STEPS
Software defined networking represents an unparalleled innovation for IT network professionals managing enterprise networks. It's flexible, smart, and highly automated. If you'd like to learn more about SDN, why you need it and the promises it delivers to a modern enterprise, we invite you read our white paper, "Software Defined Networking - The Next IT Paradigm of Promise."










