 The threat landscape is ever evolving, and today’s enterprises face more cybersecurity challenges than ever. Between the rise of cloud computing, increased utilization of internet of things (IoT) devices, and the distributed nature of today’s workforces, the attack surface has never been larger.
The threat landscape is ever evolving, and today’s enterprises face more cybersecurity challenges than ever. Between the rise of cloud computing, increased utilization of internet of things (IoT) devices, and the distributed nature of today’s workforces, the attack surface has never been larger.
To keep ahead of cybercriminals and ensure data is secured, enterprises need security that’s built-in at the foundational level of the digital environment, not tacked-on later.
Common challenges for server security
While virtualization has become increasingly important for enterprise success, it has also created additional avenues for attack. In terms of server security, the fewer physical servers an organization has, the more important it is that each of those servers is secure. If an attack is successful, the fallout is much more severe in these scenarios than times past.
The bottom line is that as enterprises prioritize digital transformation efforts and more and more data is kept in fewer physical locations, protecting that data becomes mission critical.
For this reason, Dell EMC has prioritized cyber resiliency when designing its servers. Dell EMC has identified the following four features as key to providing data center security.
1. Built-in vs. bolted-on security
As previously stated, security must be included in the overall design of the server to offer comprehensive protection. To this end, Dell EMC builds protection into the PowerEdge server architecture, ensuring security from server deployment to retirement.
2. Security by design
Comprehensive server security shouldn’t just stop attacks, it should also include the functionality to determine when an attack has succeeded and provide data recovery. Dell EMC’s PowerEdge servers feature its powerful hardware root of trust, which provides security by authenticating BIOS and firmware during the server boot process.
3. Server integrity from silicon to system
Whenever issues threaten your environment, whether they be a cybersecurity attack or software bugs, they must be identified and dealt with quickly to minimize their impact. Dell EMC’s iDRAC, integrated into the PowerEdge servers, continuously monitors the system and sends alerts regarding changes to configuration parameters across the environment.
4. Rapid recovery
As previously mentioned, comprehensive server security includes the tools for rapid recovery. Dell’s PowerEdge servers include built-in automatic recovery, which will restore the server to a trusted state in the event of a cyberattack, even if the attack is made directly against the BIOS, firmware, signed drivers, or any signed components.
[Featured Video]
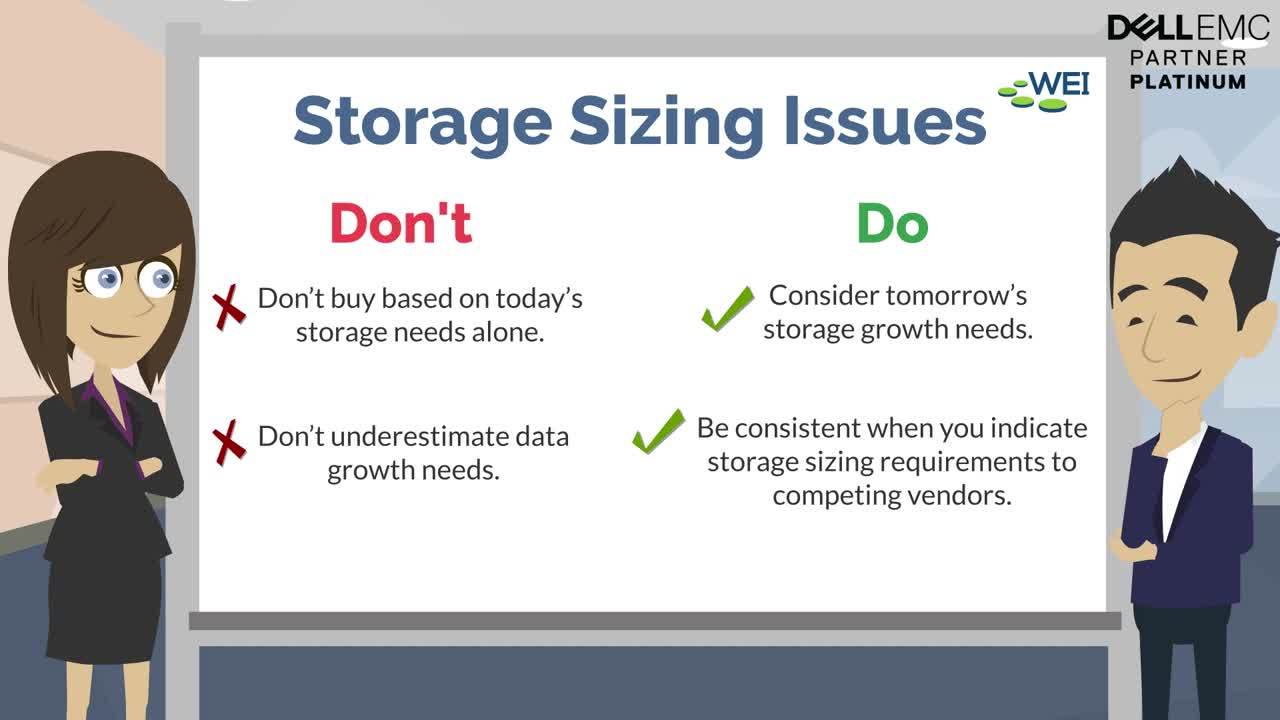
Explore these Dos and Don’ts of Enterprise Storage
Three requirements for your path to security
The requirements for comprehensive server security can be broken down into three categories: protect, detect, and recover. Dell’s PowerEdge server offers a number of features and key components that deliver security in these key areas.
1. Protect
When it comes to protection, Dell EMC utilizes the aforementioned hardware root of trust, as well as cryptographically signed firmware which enforces a secure platform environment. Self-encrypted disks (SEDs) are utilized to protect data at rest and the iDRAC offers agent-free management that ensures server security throughout the environment.
2. Detect
In terms of detection, Dell EMC employs physical intrusion detection to identify any physical tampering of servers, as well as drift detection, which offers continuous detection of configuration and firmware changes. Dell’s PowerEdge servers also log every event and provide alerts, including recommended actions in the event of an issue, further ensuring end-to-end server security.
3. Recover
Ensuring that data can be recovered in the event of an incident is just as important as preventing it in the first place. To this end, Dell EMC PowerEdge servers offer seamless recovery to a protected BIOS image after a security breach or other event. Automatic restoration of server configuration after hardware updates or replacement is also offered, reducing time and resources spent on administration during upgrades.
Through Dell EMC’s security-centric infrastructure, enterprise can improve the cyber resiliency of their infrastructure, make data more available, and improve productivity throughout the enterprise.
Are you looking to improve your server security?
Whatever your enterprise’s specific situation, Dell EMC can deliver the protection you need to keep your data safe. Through the Dell EMC PowerEdge server portfolio, enterprises can simplify management and reduce costs, while ensuring end-to-end data protection, attack detection, and data recovery.
Next Steps: Dell EMC VxRail also comes out of the box with built-in security thanks to their PowerEdge server. VxRail has also been a leading hyperconverged system for enterprises across all industries, and for several good reasons, 10 of them in fact! Find out why IT leaders turn to VxRail to achieve their data center modernization goals in our tech brief, “Top 10 Reasons Why Customers Choose VxRail.”











