 One of the natural traits of people is to long for the “good old days.” It is that magical era we tend to memorialize as a time when things were simpler and uncomplicated. That is certainly true of network security. Remember when all you had to do was simply protect your network perimeter? Can you even define what your network perimeter is anymore? It’s not so easy to answer that question today.
One of the natural traits of people is to long for the “good old days.” It is that magical era we tend to memorialize as a time when things were simpler and uncomplicated. That is certainly true of network security. Remember when all you had to do was simply protect your network perimeter? Can you even define what your network perimeter is anymore? It’s not so easy to answer that question today.
So many enterprises incorporate hybrid architectures that integrate multiple clouds to host applications and other resources. Others consist of a WAN mesh encompassing sometimes hundreds of sites. Now consider all of the incoming VPN connections from employees and partners. On top of that is the plethora of IoT devices that continue to spout throughout your enterprise. Finally, think about the perpetual cat and mouse game that hackers play with your users through phishing attacks and malware. In other words, it’s complicated today—very complicated. Are you starting to reminisce about enterprise security 20 years ago?
The realization that there is no longer a single perimeter leads to a sobering recognition; that many networks are operating under the deceptive premise that traffic inside the perimeter (whatever that is) is no more trustworthy than traffic from external sources. Vulnerability and exploits are everywhere. While digital transformation has created limitless opportunities, it has also created an equal number of exploitable vulnerabilities. When applications can reside anywhere and employees can work from anywhere, the traditional approaches of managing and securing a defined network perimeter becomes irrelevant. What is required is a Next Generation Firewall Solution that is designed for a digitally transformed world.
Visibility and Automation across the Enterprise Fabric
The typical network fabric extends far beyond the switches of your data center. By 2020, approximately 83 percent of all enterprise workloads will be in the cloud. The reality is that your security fabric must cover your expansive enterprise because an increased network fabric results in an increased attack surface. That means your firewall security solution must have the same expansion capability as your enterprise in order to protect your entire attack surface.
Fortinet FortiOS 6.2 can power your entire enterprise fabric to secure all areas of your network. This applies to complicated SD-WAN topologies as well as integrated multi-vendor ecosystems. For instance, FortiOS has a broad array of API driven fabric connectors that provide integration and orchestration with multiple SDN, cloud, management and partner technology platforms as is shown in the screenshot below.
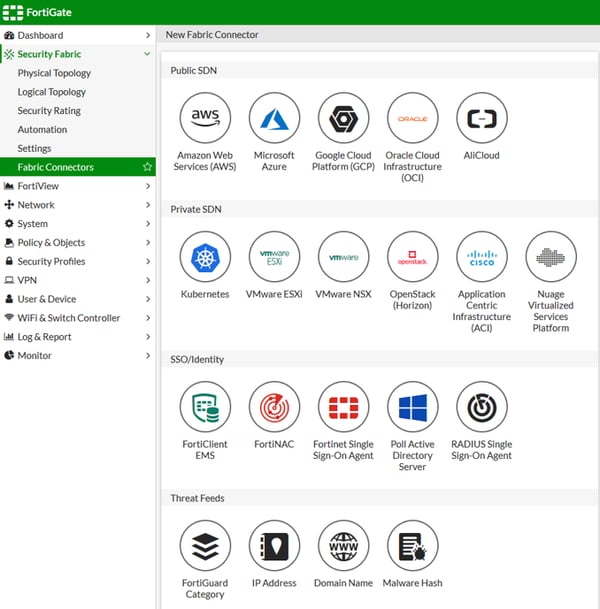
These fabric connectors can provide turnkey connectivity for Fortinet enterprise security fabric in only minutes in order to integrate all areas of your distributed enterprise. It’s more than just integration though.
3 Benefits of Fortinet Security Fabric
-
Visibility - It is difficult to protect what you cannot see. FortiOS 6.2 provides visibility across the entire fabric of your enterprise so that there are no security or discernibility gaps in your network. This includes multi-cloud environments as well as complicated multi-branch SD-WAN topologies. Comprehensive visibility across the full spectrum of your distributed enterprise helps you tie applications, devices and workflows together in order to secure any and everything.
-
Simplification - Deployment is simplified by using pre-integrated, pre-validated solutions. Eliminating complexity is important because 90 percent of cyberattacks are caused by human error or behavior. This simplicity is driven by single pane of glass management that gives you visibility and control across the entire enterprise fabric. This allows for simple, but complete control.
-
Automation – The ability to adapt to dynamically changing network configurations and intrinsically respond to real time detected threats is imperative today because manual intervention cannot react in time to the advanced threats today. In this new threat era, seconds count. Automation includes the ability to quarantine compromised devices, partition network segments, orchestrate policy enforcement, and eradicate malware.
Unified Threat Management across Your Enterprise Fabric Frontier
Network architects are busting up silos across the data center today. The three data center components of compute, networking and storage no longer work in isolation. Instead, they are being software defined in order to work collaboratively together. If only your security tools could work synchronously together. Today’s enterprises host an average of 75 security products. Often times these solutions work in isolation from one another, preventing security admins from leveraging their combined capabilities.
FortiOS 6.2 seamlessly weaves all of its enclosed tools, features and capabilities into an integrated, cohesive and coherent security fabric. In order to protect your vast network frontier, FortiOS 6.2 incorporates scalability and shared AI driven intelligence to keep pace with an ever evolving world of malicious threats. This shared approach isn’t just limited to the tools that exist within the FortiOS security fabric. It incorporates AI driven security based on the data that FortiGuard Labs receives from more than 4 million firewalls across the world.
FortiOS is the Next Generational Solution Your Enterprise Needs
As time goes on, we tend to outgrow things. It is a fact of life. Your network is no different. Your security fabric must grow in sync with your enterprise. That requires agility and scalability, the same facets that companies are diligently pursuing in quest of their digital transformation. Because of its inherent adaptedness and flexibility, FortiOS is the core you need for your security fabric that can safeguard the enterprise fabric you have today, and the ever-growing fabric of tomorrow.
NEXT STEPS: Are you considering SD-WAN for your distributed enterprise? Grab a copy of the FREE checklist from our friends at Fortinet to learn more about why their secure SD-WAN solution might be the right fit for your organization.












