 Enterprise mobility is a key strategic component of any digital transformation strategy. When handled properly, it can help you better serve your customers through both mobile devices and laptops, while also helping your organization clarify its technology efforts with a “digital-first” mindset.
Enterprise mobility is a key strategic component of any digital transformation strategy. When handled properly, it can help you better serve your customers through both mobile devices and laptops, while also helping your organization clarify its technology efforts with a “digital-first” mindset.
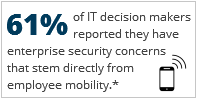
While mobility is set to play an increasingly important role in business, there are many reasons for enterprises to be cautious as well, chief among them are security concerns. How do you balance your workforce transformation to ensure that productivity and security are both equally accounted for? While the answer to this question may extend beyond the scope of a single blog post, we can look at some of the fundamental questions you’ll need to answer to ensure your journey to increased mobility begins in the best possible way.
Do You Have Access to the Right IT Resources?
At the earliest stages, you should define what your organization expects from its mobility strategy. What type of connectivity do employees need to achieve optimal productivity? Are your business processes and current technology solutions prepared for the increased activity that will come with heightened availability to your users?
This initial phase should also include reviewing the capabilities of your IT staff to make sure they’re prepared for the complexities of keeping your mobile network secure. In even small and midsized companies, there are often enough heterogenous mobile devices to make testing and supporting all of them equally impossible—especially when your IT department is already busy with the day-to-day management of infrastructure and employee support. This is doubly true for organizations that plan on embracing bring your own device (BYOD). BYOD exacerbates many of the security issues inherent in enterprise mobility, like increasing public exposure of company data on unsecured networks. It can also present new vulnerabilities, such as the accidental deletion or transmission of company data from personal devices. To avoid problems down the road, companies that plan on employing a BYOD strategy should consider ways to remediate these concerns early in the planning process.
If your internal staff aren’t confident that they can handle these challenges, it may be helpful to seek outside assistance from an IT solutions provider with experience in mobile security. An external partner who has experience building mobile security solutions can help you avoid costly mistakes, roll-out the solution as quickly as possible, and ensure you achieve the maximum ROI from your investment.
Carefully Audit Both Your Hardware and Software
In order to ensure that your enterprise mobility strategy is a success and won’t require costly revisions after its initial deployment, determine which devices and services you’re going to accommodate in your solution and prioritize these devices and platforms in all subsequent planning phases.
Next, thoroughly review the software that’s going to be used on mobile devices, as well as all your desktop- or server-based applications that will interact with your mobile devices. While many software vendors have started building mobile capabilities into their products, many popular line of business applications still require software fixes to achieve true mobile functionality. For applications that provide back-end data to other applications, such as business analytics or CRM software, incompatibilities may be particularly damaging, potentially derailing an entire mobile strategy. If your current software isn’t ready for increased employee mobility, seek alternatives that may fit better into your new mobile strategy or talk with WEI, we specialize in building customized solutions for our clients.
Whether you choose new software or to update a legacy solution, always keep one eye firmly on overall system security. There are many ways that a mobile application can threaten the security of your company network, ranging from weak or non-existent encryption, to poor identity or access management controls, or unsecured APIs that give hackers a path to bypass network security.
Once you’ve determined the optimal mix of hardware and software for your mobile employees, you can then start to choose a security platform. The latest generation of mobile security platform, called enterprise mobility management (EMM), will not only help protect your mobile devices, applications, and data against cyber threats, but will also reduce your IT department’s workload by providing service portals that allow your employees to self-manage their mobile devices. While there are lots of EMM vendors to choose from, standouts like VMware Airwatch and Microsoft Intune are good places to start the vetting process.
WEI is Your Expert in Mobile Security
WEI has a range of resources and services that will benefit both companies that are looking to launch a new enterprise mobility initiative or increase the scale or security of their existing program.
WEI offers a variety of services to streamline your enterprise mobility program, such as custom imaging, break/fix, large scale rollouts/deployments, QA testing, and device asset management—all while ensuring security and end user productivity. Contact us today to discuss your enterprise mobility strategy.
NEXT STEPS: For more information about the current state of enterprise mobility, and for insight into how other companies are tackling enterprise mobility challenges, please read our tech brief, "The Challenge of Supporting Today's Mobile Enterprise."













