The 2023 MITRE Engenuity ATT&CK® Evaluation results were recently released, and out of 29 participating cybersecurity vendors, only one delivered 100% protection and 100% analytic coverage with zero configuration changes and zero delayed detections.
The 2023 MITRE Engenuity ATT&CK® Evaluation results were recently released, and out of 29 participating cybersecurity vendors, only one delivered 100% protection and 100% analytic coverage with zero configuration changes and zero delayed detections.
Many cybersecurity analysts familiar with ATT&CK evaluations have heard claims of 100% security from many participating vendors, but once you dig down, it becomes clear that these solutions have at least one detection and/or prevention event. Only one vendor is exempt of this, but you will have to wait for that reveal. For now, let’s summarize who MITRE is and why this annual evaluation is so incredibly relevant.
What Is The MITRE Framework?
Organized by the MITRE Corporation, this globally recognized knowledge base stands for Adversarial Tactics, Techniques, and Common Knowledge. It catalogs cyber adversary tactics and techniques drawn from real-life observations, essentially serving as a comprehensive "playbook” that offers insights into the strategies of cyber adversaries and their attack methodologies. Just like a head coach and their players must be in synch with their team’s offensive and defensive playbook, security analysts must thoroughly understand the tactics, techniques, and procedures (TTPs) detailed in the MITRE framework. Presently, the framework encompasses over 500 distinct TTPs employed by identified threat groups.
The MITRE ATT&CK® framework is extensively utilized by internal teams, security operations centers (SOC), managed security service providers (MSSPs), product vendors, researchers, and red team personnel. Rather than solely relying on signature identifiers, the framework emphasizes the behavior patterns of an attack. This is key because as attackers continually evolve their tactics, signature-based defenses often lag in detection and prevention.
The MITRE ATT&CK® framework is a dynamic, constantly updated resource that keeps pace with these evolving TTPs to provide organizations with current information critical for maintaining a secure IT landscape.
What Are The MITRE Enterprise ATT&CK® Evaluations?
The MITRE Enterprise ATT&CK® Evaluations are annual assessments designed to assess the effectiveness of cybersecurity products against known TTPs, all of which are outlined in the ATT&CK® framework. During the MITRE Enterprise ATT&CK® Evaluations, products from participating security vendors undergo a sequence of rigorous tests designed to emulate the tactics of established threat groups. MITRE’s Engenuity red teams orchestrate these simulated attacks, challenging cybersecurity solution providers to showcase their product's capabilities in three key areas:
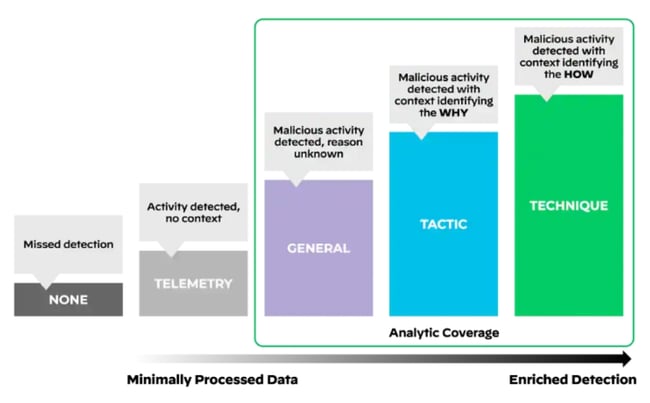
- Visibility: Assessing the extent of a solution's observational scope.
- Detection: Evaluating the solution's ability to accurately recognize malicious actions.
- Prevention And Response: Determining how effectively a solution can prevent and react to these threats.
The outcomes of these evaluations offer valuable insights into each product's proficiency in identifying, blocking, and reacting to simulated attacks that mirror real-world scenarios. It is important to note that these evaluations are not competitive in nature. Rather, their focus is to provide clarity and insight into the real-world effectiveness of security products. MITRE Engenuity does not assign scores, rankings, or ratings and leaves evaluation results to be sorted out by the public.
2023 marked the fifth iteration of this event as the MITRE Engenuity red team chose to emulate Turla, a highly sophisticated and well-resourced Russian threat group. Turla’s victims span more than 45 countries, and targets have included government agencies, military groups, diplomatic missions, and research/media organizations.
Turla’s covert exfiltration tactics, custom rootkits, elaborate command-and-control network infrastructure, and deception tactics made it a sophisticated option for the MITRE evaluation. Kudos goes to the entire MITRE Engenuity team for executing this emulation, as 2023 was significantly more challenging than past years were.
Palo Alto Networks’ Cortex XDR Shines In MITRE Evaluation
It is normal protocol for many vendors to proclaim success after completing this rigorous, annual evaluation, but only Cortex XDR from Palo Alto Networks (the same technology that Cortex XSIAM is built on) demonstrated 100% analytic detection and prevention without the need of any configuration changes or delays.
A blue team was assigned the task of protecting against the red team’s tactics using the solutions provided by participants. In the case of Cortex XDR, they deployed the Cortex XDR Pro for Endpoint agent on both Windows and Linux endpoints. No additional solutions were deployed. Other than the enabling of malicious file quarantining and the option to treat grayware as malware, Cortex XDR was configured with default, fresh-out-of-the-box settings. No special steps were taken by the blue team.
Out of the 29 vendors participating, Cortex XDR uniquely identified all 143 techniques and successfully countered 129 attack steps, a testament to its robust protection capabilities. This impressive performance underscores Cortex XDR’s potential in helping security teams defend enterprises and manage service clients against the dynamic and evolving threat landscape. You can read more about Cortex’s dominant performance in the 2023 evaluation here.
If Cortex can achieve perfection under the most demanding of circumstance with zero configuration changes, imagine how it could aid your enterprise’s cybersecurity team against the evolving threat landscape. If you want to learn more about how Cortex XDR can secure your own enterprise, contact a WEI cybersecurity specialist today.